Trezor Login – A Complete Guide to Accessing Your Hardware Wallet Safely
Master the art of securely logging into your Trezor hardware wallet. From connecting your device to entering your PIN and using passphrases, this guide walks you through every detail of the Trezor Login process — ensuring your crypto stays safe, private, and under your full control.
Your
Crypto
Vault
Crypto
Vault
Understanding Trezor Login
Unlike typical logins that rely on a password stored online, Trezor Login is an offline, physical authentication method. Your Trezor device serves as a digital vault that holds your private keys securely inside its chip — away from the internet and potential hackers. To access your wallet, you must physically confirm every login and transaction on your device. This process forms the foundation of hardware wallet security.
Why Trezor Login Is Critical
Every crypto transaction must be signed. By requiring a physical login, Trezor ensures that hackers can’t sign or approve transactions without the actual device. Even if malware infects your computer, your crypto remains protected. Your login is your shield — digital yet tangible.
Quick Trezor Login Facts
- PIN entry is done securely on your computer interface, guided by randomized on-device numbers.
- A passphrase can create hidden wallets for extra privacy.
- Firmware updates in Trezor Suite enhance login safety and usability.
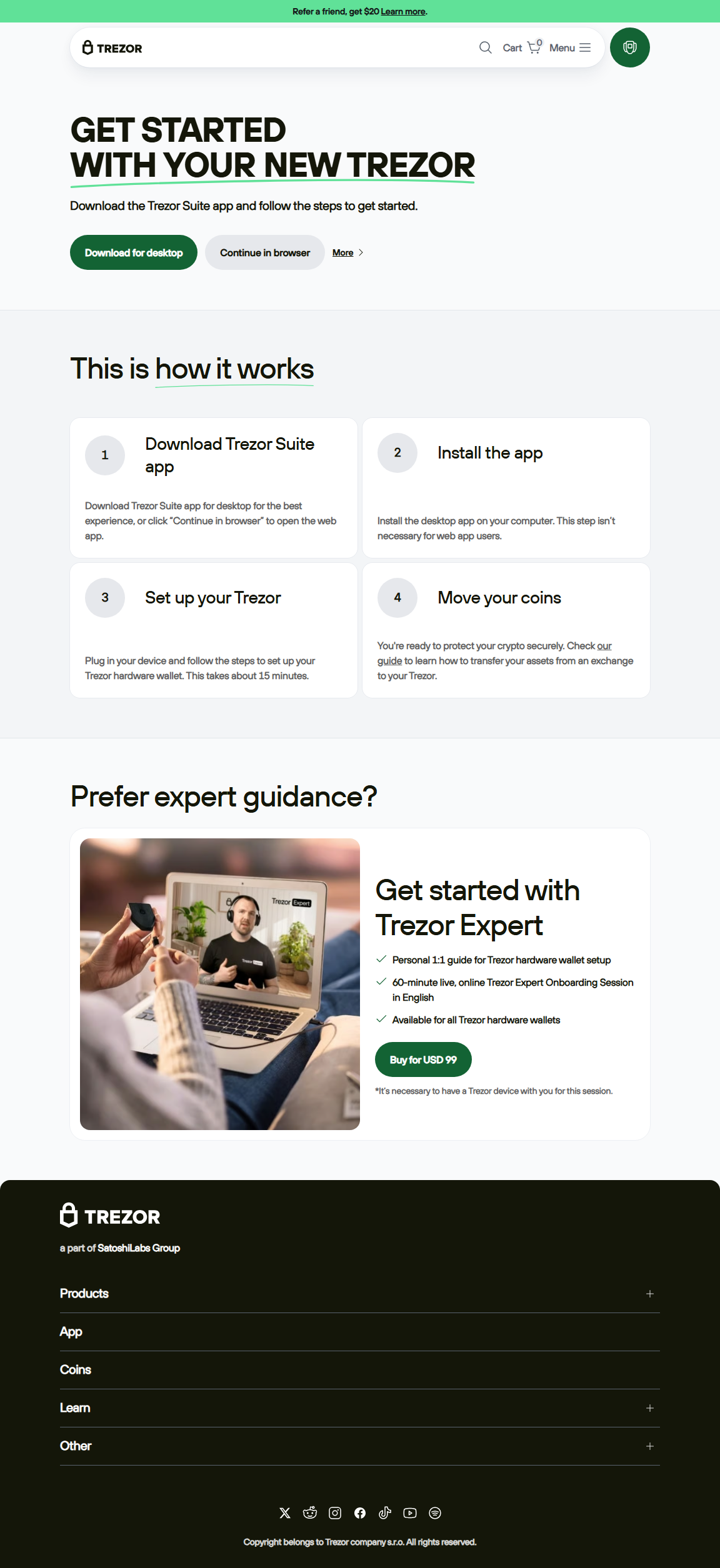
How to Perform a Secure Trezor Login (Step-by-Step)
Step 1: Connect Your Trezor Device
Plug your Trezor hardware wallet into your computer using the provided cable. Ensure it’s directly connected, avoiding hubs or adapters that may cause connection errors.
Step 2: Open Trezor Suite
Trezor Suite is the official app for managing your crypto portfolio and device. Once launched, it automatically detects your connected device. If using a web version, make sure to allow USB permissions in Chrome or Edge.
Step 3: Enter Your PIN
The PIN is your local protection layer. You’ll see a blank grid on your computer and a randomized keypad on your Trezor. Match the correct numbers using the device’s display — this design prevents keyloggers from capturing your input.
Step 4: Confirm the Connection
Trezor will display a confirmation request to ensure you’re connecting to a trusted application (like Trezor Suite). Always verify the fingerprint hash or connection prompt before approving.
Step 5: Optional – Enter a Passphrase
Advanced users can enable a passphrase, adding an extra “invisible layer.” Each unique passphrase generates a separate wallet derived from your recovery seed. Remember: lose the passphrase, lose access to that hidden wallet.
Think of It Like a Physical Safe
Imagine your Trezor as a high-security safe. Your PIN is the key, and the passphrase is an additional secret compartment inside. Even if someone finds your safe, without both the key and the secret compartment code, they can’t open it. This layered security model defines why Trezor is one of the safest wallets available.
PIN vs Passphrase vs Recovery Seed
Security Feature
PIN
Passphrase
Purpose
Device access
Creates hidden wallet
If Lost
Device reset required
Hidden wallet inaccessible
Stored?
Inside Trezor
Entered manually each time
Troubleshooting Trezor Login Issues
Device not detected: Try a different USB port or cable. Reinstall Trezor Bridge or update Suite. Restart both the computer and the device.
PIN forgotten: After multiple failed attempts, Trezor wipes itself automatically. Restore your wallet using your 12/24-word recovery seed.
Hidden wallet not opening: Ensure you’re using the exact same passphrase (case-sensitive). Even a small typo generates a completely different wallet.
PIN forgotten: After multiple failed attempts, Trezor wipes itself automatically. Restore your wallet using your 12/24-word recovery seed.
Hidden wallet not opening: Ensure you’re using the exact same passphrase (case-sensitive). Even a small typo generates a completely different wallet.
“True security isn’t about locking doors — it’s about making sure only you have the keys. The Trezor login flow is designed exactly for that.”
— Crypto Security Insight
Frequently Asked Questions About Trezor Login
Q: Can I log into Trezor without the device?
A: No. The device is essential for authentication. Without it, you can’t access or sign transactions — this is by design for maximum security.
Q: Is Trezor Suite mandatory for login?
A: While Suite provides the official interface, you can use other apps like MetaMask or Electrum via Trezor Connect. However, Suite ensures the most seamless and secure login experience.
Q: Can I change my PIN after setup?
A: Yes. Go to “Device Settings” in Trezor Suite and choose “Change PIN.” You’ll confirm this on the device itself.
Q: Is the passphrase stored anywhere?
A: No. It’s never saved on the device or in software. You must enter it each time you access your hidden wallet — making it an ultra-secure access method.
Trezor Login Safety Checklist
✅ Connect using the original cable only.
✅ Use Trezor Suite desktop version when possible.
✅ Enter PIN only within the official interface.
✅ Verify all actions on your device screen.
✅ Store your recovery seed offline in a safe place.
✅ Never share your PIN, passphrase, or seed with anyone.
✅ Use Trezor Suite desktop version when possible.
✅ Enter PIN only within the official interface.
✅ Verify all actions on your device screen.
✅ Store your recovery seed offline in a safe place.
✅ Never share your PIN, passphrase, or seed with anyone.
Conclusion – Your Security Starts with a Proper Trezor Login
The Trezor Login process combines physical verification with digital encryption — offering unmatched safety for your crypto assets. Each action, from entering your PIN to confirming on-device prompts, reinforces your control. By mastering this login routine and understanding its layers, you minimize human error and build long-term peace of mind in the crypto space.
Stay vigilant, stay offline when possible, and trust only what your Trezor device shows. That’s the real login mindset.